Managed Hosting, Care Plans & WordPress Support for UK Businesses
From £50/month managed hosting to full-service care plans at £250 or £500/month — hosting, updates, security, development, and expert support included. Focus on running your business while we handle your website.
Your site monitored, maintained & secure - around the clock
From daily off-site backups to real-time malware scanning, our managed WordPress hosting handles everything so you never have to think about it.
You'll always have a live dashboard view of your site health, and we'll reach out proactively if anything needs attention.
Our Services
From managed hosting to complete rebuilds, we offer precision-crafted solutions for businesses in Shropshire and across the UK.
Managed WordPress Hosting
Enterprise-grade hosting with daily backups, security monitoring, performance optimisation, and expert support - all included from £50/month.
Learn more about Managed WordPress HostingWordPress Care Plan
Everything in Managed Hosting plus 4 hours monthly development, proactive improvements, priority support, and technical consultation from £250/month.
Learn more about WordPress Care PlanWordPress Care Plan Pro
Increased development capacity, conversion optimisation, advanced performance, integration support, and strategic guidance from £500/month.
Learn more about WordPress Care Plan ProNew Websites
Custom-designed, high-performance websites built for conversion. Bespoke to your brand, optimised for search, and built to last.
Learn more about New WebsitesWebsite Refreshes
Modernise your existing site with improved UX, faster load times, better mobile experience, and stronger conversion rates.
Learn more about Website RefreshesCustom WordPress Development
Ad-hoc development, custom functionality, plugin builds, API integrations, and complex WordPress work when you need it.
Learn more about Custom WordPress DevelopmentTried & Tested Across Multiple Industries
We build bespoke WordPress sites for every type of business — from tradespeople and retailers to professional firms and community organisations.
Trades & Construction
Builders, electricians, plumbers and more
Professional Services
Solicitors, accountants, estate agents
Beauty & Personal Care
Hair salons, nail bars, tattoo studios
Food & Drink
Restaurants, cafes, takeaways, butchers
Retail & Home
Shops, jewellers, gardeners, cleaners
Community & Education
Schools, charities, nursing homes
Business & Tech
Developers, manufacturers, SMEs
Health & Medical
Therapists, nursing homes, clinics
10+ years optimising websites in Shropshire
Not just another web developer. I have professionally worked as a designer, developer and UX analyst with Google-certified UX expertise - I know what turns visitors into customers.
Every website I create is informed by data, user research, and over a decade of experience across 15+ industries. No guesswork - just proven results.
 Google Mobile UX
Google Mobile UXCertified
 Google Analytics
Google AnalyticsCertified
"Adam did a fantastic job upgrading an existing site - I was 'wowed' with a mock up he produced (knocked my socks off!) He really has an eye for making things look stunning and visually pleasing! Very pleased with the website he has produced for me and will be recommending him to my colleagues."
Recent projects & hosting clients
A selection of websites we've built, redesigned, or brought onto our managed hosting platform.
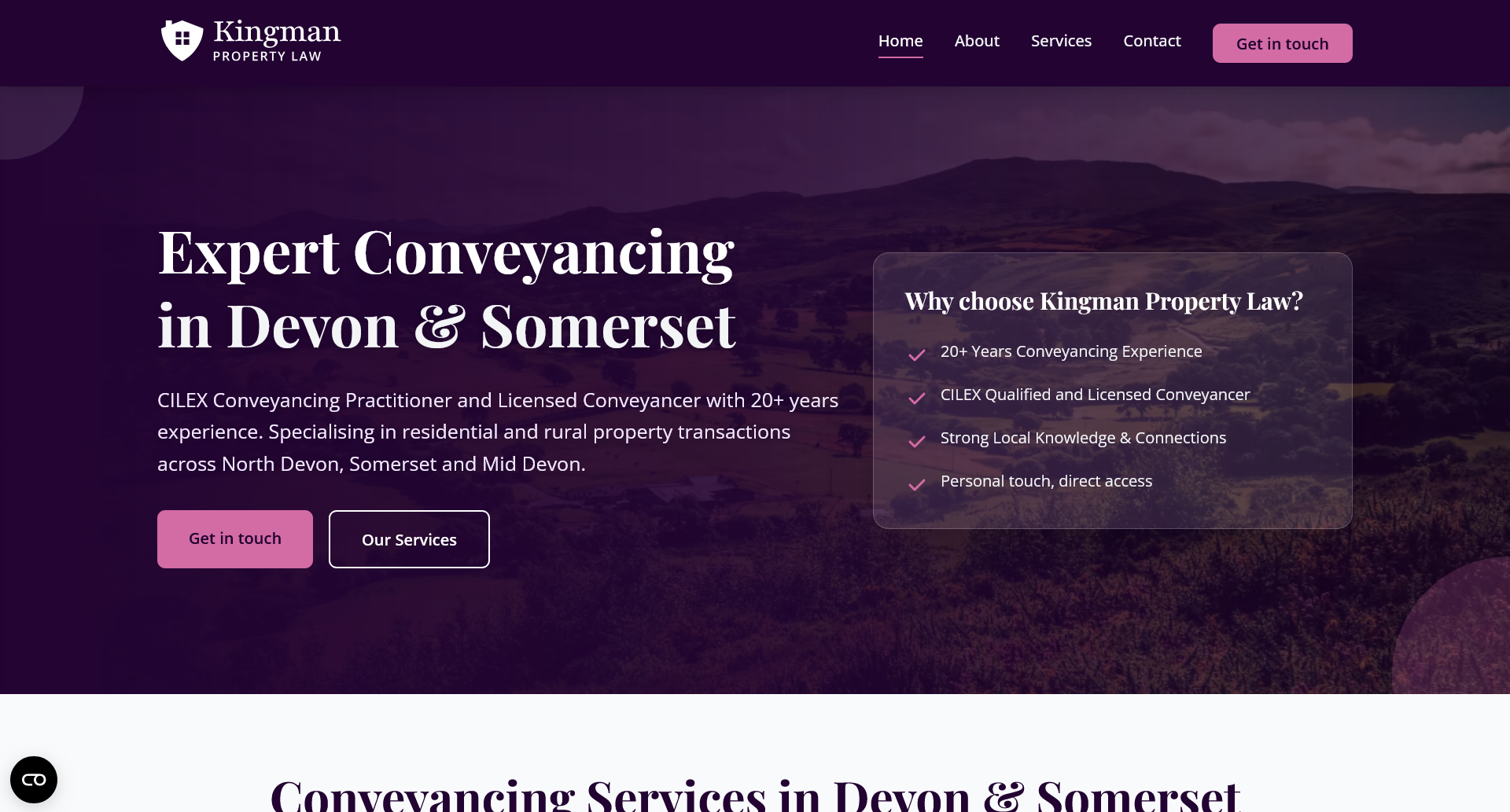
Kingman Law
Legal Services
Professional legal services website for a property law and conveyancing firm covering Devon and Somerset.
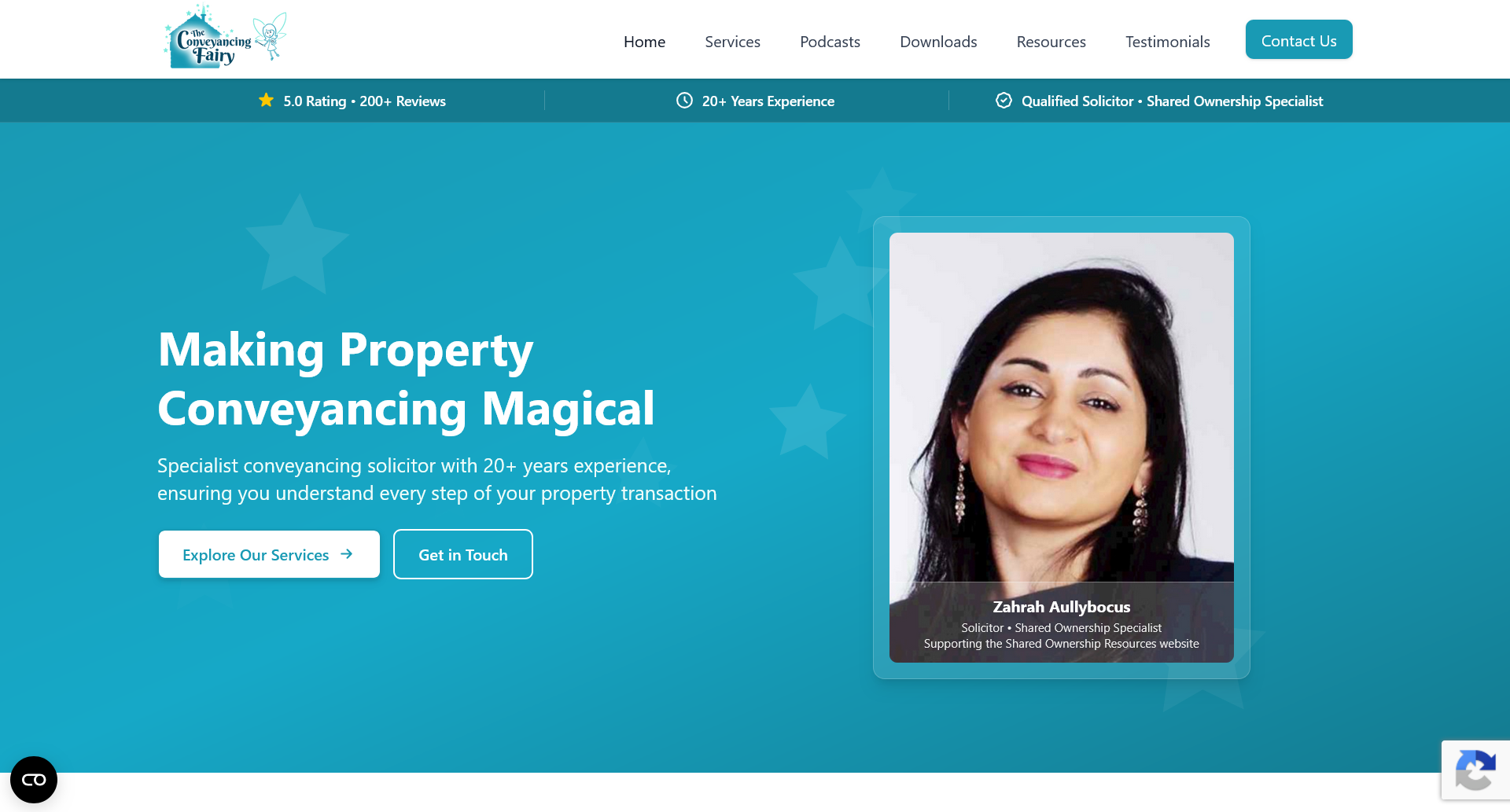
Conveyancing Fairy
Legal Services
Clean, conversion-focused website for a specialist residential conveyancing service, built to generate enquiries.
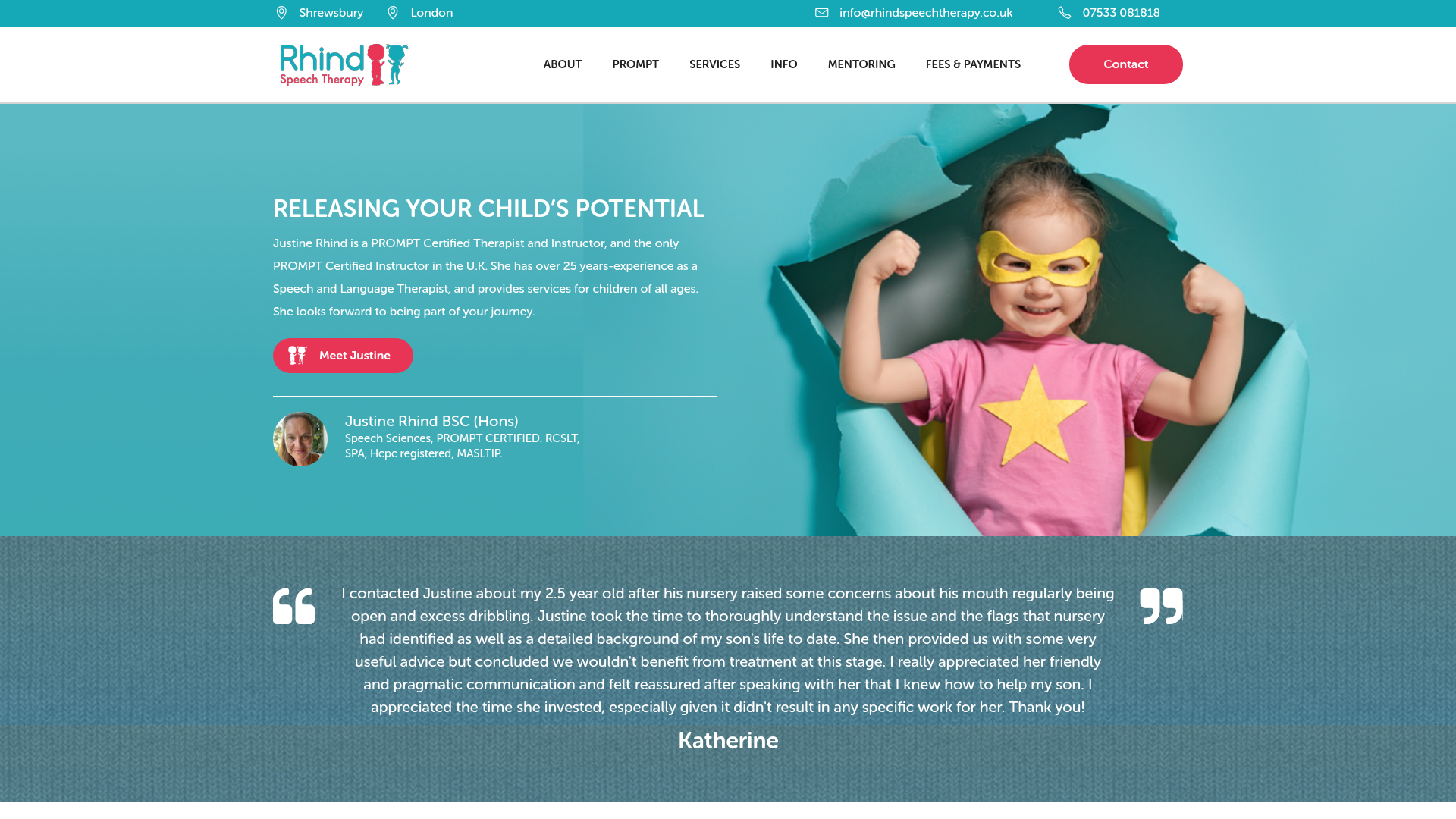
Rhind Speech Therapy
Healthcare
Managed WordPress hosting for a PROMPT-certified speech and language therapist with clinics in Shrewsbury and London.
What's included on every website
Analytics & Tracking
GA4 & Hotjar integration for deep user insights.
Security & SSL
Enterprise-grade security and encrypted connections.
Speed Optimization
Lightning-fast load times for better conversions.
Mobile Responsive
Flawless experiences across all devices.
Technical SEO
Built from the ground up for search engine visibility.
User Experience Focus
Data-driven design decisions that drive action.
Ready to start your project?
Get in touch to discuss your website requirements. We'll provide a tailored quote based on your specific needs in Shropshire or nationwide.